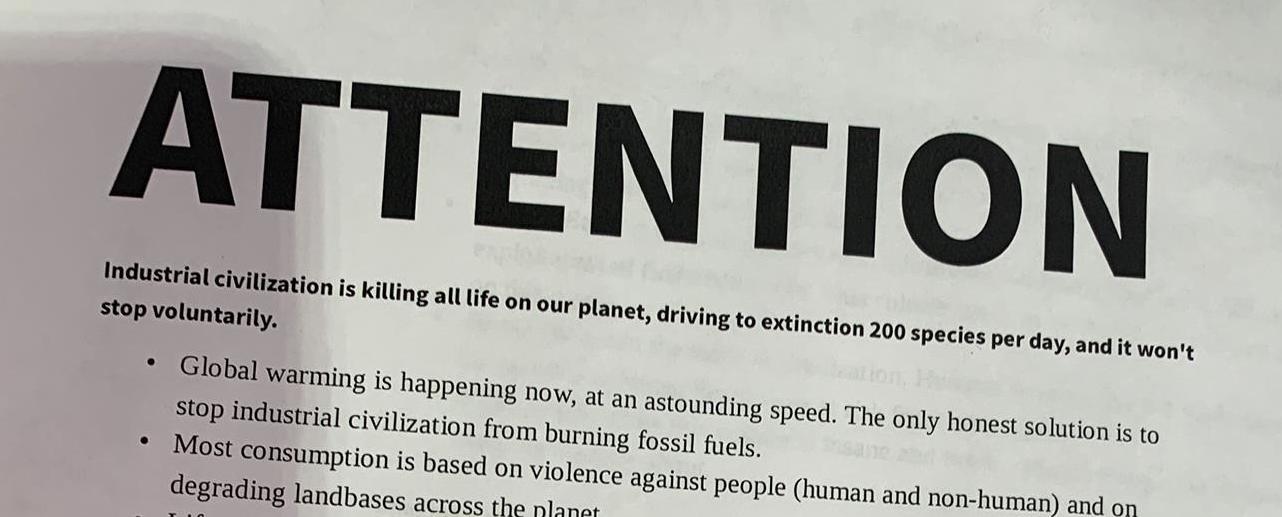
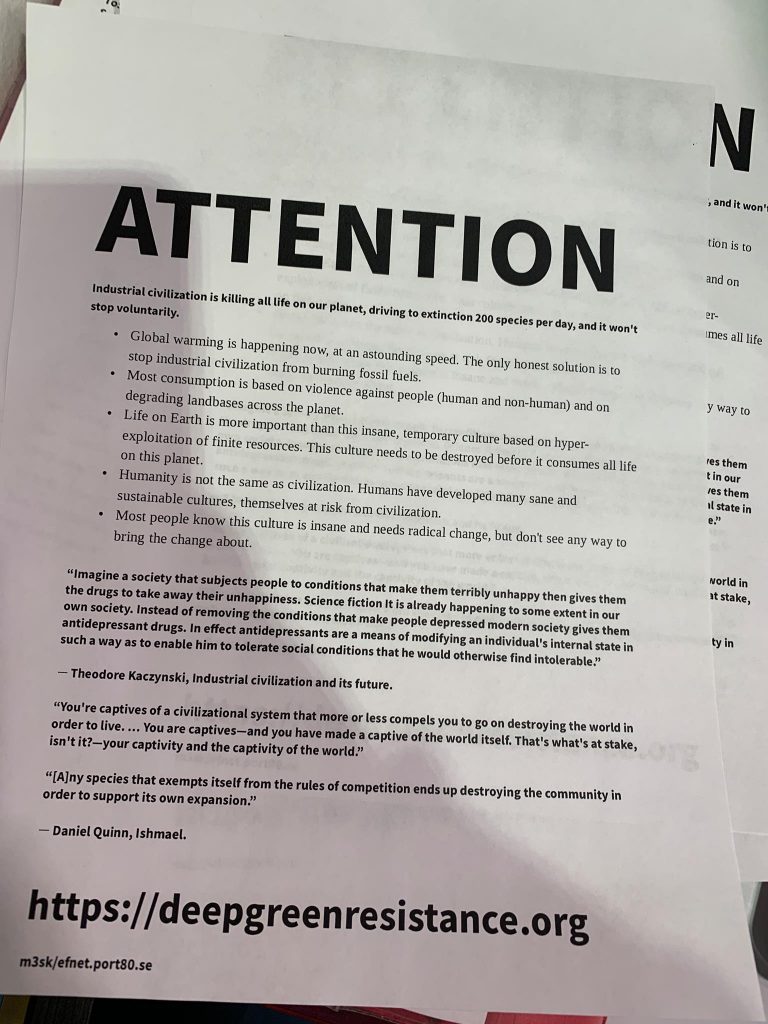
Over the past few days, several organizations from across the United States have reached out to Deep Green Resistance, letting us know about a printer exploit being used to print off DGR-themed flyers at their place of business.
These intrusions seem to be related to a larger wave of forced printings currently affecting unsecured printers (see: https://www.engadget.com/2018/11/30/pewdiepie-printer-hack-thehackergiraffe/).
We want to be very clear that these flyers are not official DGR material and have not been approved by us for publication anywhere, and certainly not on private printers without consent. The use of a Printer Exploitation Toolkit to hijack unprotected printers is unethical, unhelpful for anyone, and illegal.
At the moment, we are unsure who is behind these mailings. If this is the work of an unaffiliated DGR supporter, we ask that you please stop immediately and avoid such invasive, unhelpful behavior in the future. If these mailings are the work of agitators attempting to discredit our movement, we would ask that you please find something better to do with your time and stop wasting paper. Either way, we would like to apologize to anyone who has had to deal with this time-wasting stunt. Although we are unable to prevent every unstable or unscrupulous person from deciding to do stupid and unhelpful things, we are taking every step possible to make sure this doesn’t happen again. In the meantime, we encourage everyone – especially activists – to make sure their internet-connected devices are secure.
Here is the official recommendation on how to secure your printers against this type of attack: “Network administrators should never leave their printers accessible from the Internet and disable raw port 9100/tcp printing if not required” (more here).